The Democratization of Zero-Days and the End of Scarcity
In the past, ‘Zero-Day vulnerabilities’ were the exclusive domain of national intelligence agencies or elite hacking groups with massive budgets and advanced technical prowess. These ‘asymmetric weapons,’ traded for hundreds of thousands of dollars on the dark web, were terrifying to defenders precisely because they were so difficult to discover.
However, the times have changed. The release of Anthropic’s new model, ‘Claude Mythos,’ has completely overturned this conventional wisdom. AI has reached a stage where it can analyze complex source code in just a few hours to identify Zero-Days and even generate exploit code. Zero-Days are no longer special weapons; they have become ‘routine threats’ that anyone can mass-produce. Anthropic describes this as a ‘Watershed Moment’ for cybersecurity.We are now in an era where machines identify vulnerabilities at the speed of machines. The core of security has shifted from a competition of detection technology (who finds more) to a competition of operational agility (who remediates faster).
From the ‘Era of Detection’ to the ‘Era of Operations’: A Structural Transformation for Survival
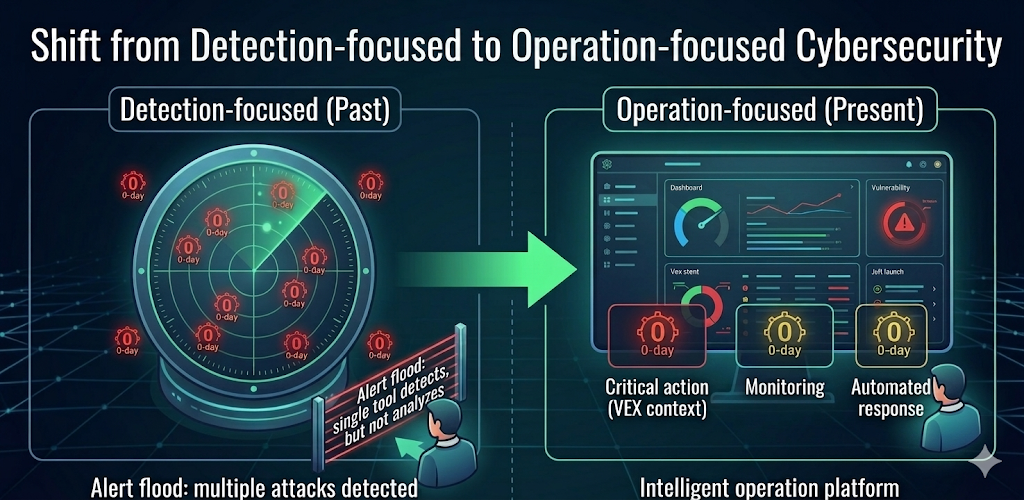
Previously, since discovering vulnerabilities required high-level expertise, the center of security lay in detection tools (scanners). However, in an age where AI accelerates analysis, detection results can become ‘noise’ rather than useful information. When vulnerabilities start pouring in, an organization must have a system capable of immediately answering the following questions:
- Real-time Visibility: Can we immediately identify which version or sub-module of our product contains the vulnerability?
- Supply Chain Scalability: Do we have visibility across the entire chain, from software received from partners to the final deliverables sent to customers?
- Context-Based Prioritization (VEX & Context): Among thousands of vulnerabilities, can we filter out the risks that are actually exploitable in our specific environment?
- Remediation Workflow: Can we automate impact analysis and remediation plans, explaining them to customers or partners before they even ask?
Detection without these capabilities does not make an organization safer; it merely leaves them dragged down by a backlog of unmanageable alerts.
SBOM: From Regulatory ‘Documentation’ to ‘Living Data’
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) defines the Software Bill of Materials (SBOM) as the fundamental ‘map’ for evaluating and remediating software risks. Yet, many companies still treat SBOMs as one-time submissions for regulatory compliance.
To survive the Generative AI era, a ‘Living SBOM Operating System’ is essential.
- Organizations must now automatically update SBOMs at the point of code changes or deployment to maintain real-time accuracy.
- Beyond listing files, they must track the entire supply chain history as software flows from Partner → Internal → Customer.
- By integrating VEX (Vulnerability Exploitability eXchange), organizations can reduce unnecessary manual labor by sharing specific status information, such as: “The vulnerability exists, but it is not exploitable in our environment.”
Securing ‘End-to-End Visibility’ Between Partners and Customers
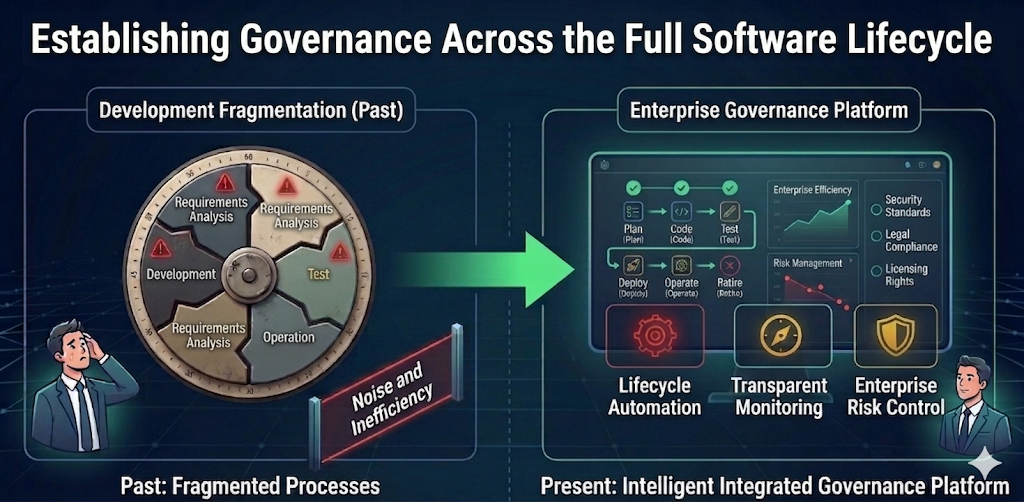
The reason supply chain security is difficult is that the answer cannot be found by looking at internal source code alone. The actual business environment is a massive chain of intertwined partner libraries, external SDKs, and products delivered to customers. If any part of this chain is broken, organizations remain trapped in a cycle of ‘Full Investigation → Manual Verification → Delayed Response’ every time a vulnerability occurs.
Now, companies must secure visibility to view every software component flowing in and out as a single, continuous stream. This will become the core infrastructure that guarantees ‘trust’ between companies, moving beyond mere security technology.
The Battlefield of the AI Era: ‘Remediation’ and ‘Explainability’
As Anthropic emphasized through Project Glasswing, the challenge ahead is not ‘how to find better,’ but ‘how to fix faster.’ Supply chain security cannot be solved by the security team alone. It must be established as an enterprise-wide operating system where development, operations, quality control, and customer support departments collaborate based on the same SBOM data.
What is needed now is not another security alert, but a system that can transform those alerts into practical action and trust.Labrador Labs presents a new standard for supply chain security in the AI era—from open-source identification and real-time SBOM management to securing software visibility across partners.
📌 Built a secure SW Supply Chain with Labrador today!
Phone: US Office +1 650-278-9253 (Mon–Fri, 9 AM–6 PM)
Email: contact@labradorlabs.ai (1:1 demo requests and pricing inquiries)
[Reference]
- Anthropic, “Project Glasswing: Securing Critical Software for the AI Era,” Anthropic, 2026.04
https://www.anthropic.com/glasswing - Carlini, N.et al.,“Assessing Claude Mythos Preview’s Cybersecurity Capabilities,” Anthropic Frontier Red Team, 2026.04
https://red.anthropic.com/2026/mythos-preview/ - CISA, “Framing Software Component Transparency: Establishing a Common Software Bill of Materials (SBOM),” CISA, 2024.10
https://www.cisa.gov/sites/default/files/202410/SBOM%20Framing%20Software%20Component%20Transparency%202024.pdf - CISA, “Minimum Requirements for Vulnerability Exploitability eXchange (VEX),” CISA, 2023.04,
https://www.cisa.gov/sites/default/files/2023-09/Vulnerability%20Exploitability%20eXchange%20%28VEX%29_508c.pdf

